blog
Upgrade Azure Active Directory Connect fails with unexpected error
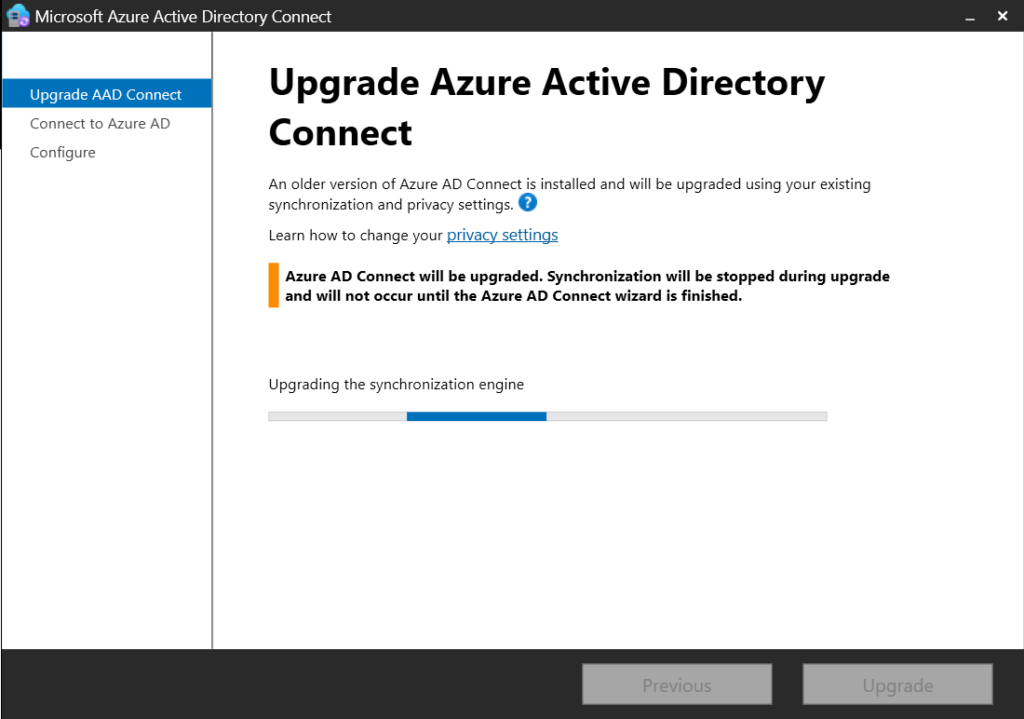
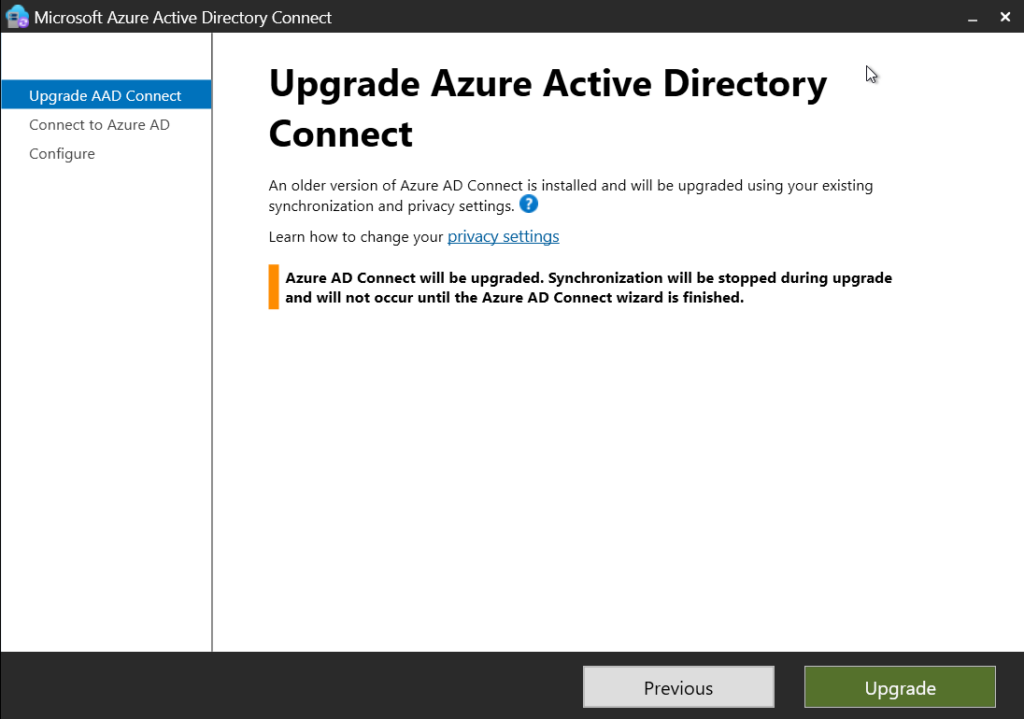
Today, I made the decision to upgrade my test environment and update the version of Azure AD Connect to the latest one. The process is usually simple: download a new MSI, run it, click next a few times, enter the credentials for your Global Admin, and you're finished. However, this time, I encountered an error.
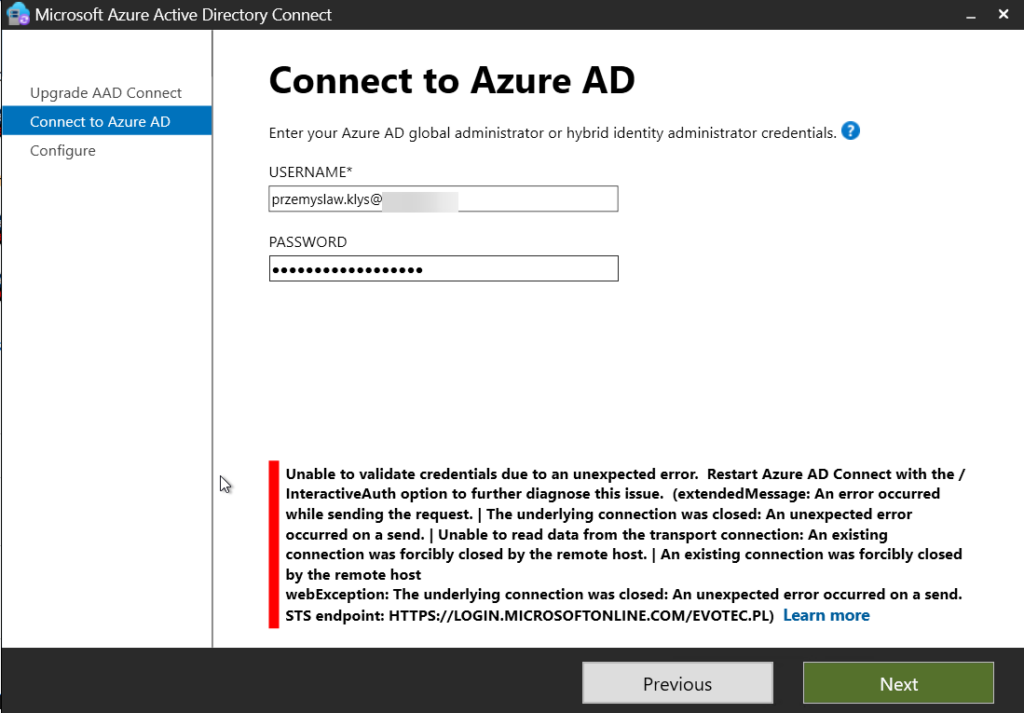
💡 Problem description
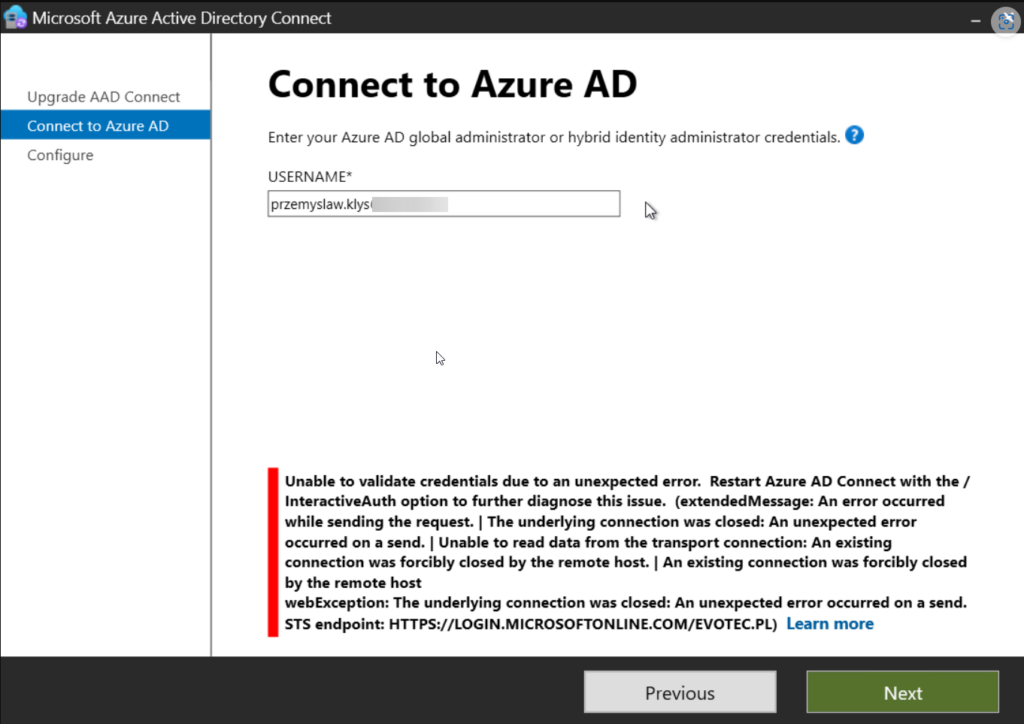
Unable to validate credentials due to an unexpected error. Restart Azure AD Connect with the /InteractiveAuth option to further diagnose this issue. (extendedMessage: An error occurred while sending the request. | The underlying connection was closed: An unexpected error occurred on a send. | Unable to read data from the transport connection: An existing connection was forcibly closed by the remote host. | An existing connection was forcibly closed by the remote host webException: The underlying connection was closed: An unexpected error occurred on a send. STS endpoint: HTTPS://LOGIN.MICROSOFTONLINE.COM/XXXXXXX)
💡 Solution
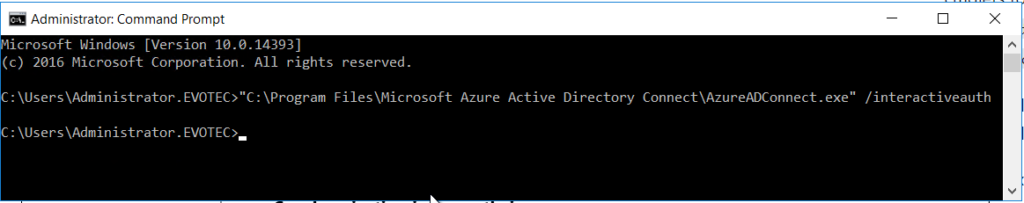
At first, I thought the solution to this problem was quite simple—due to authentication changes, one needs to start the upgrade process with InteractiveAuth, as it will most likely require MFA. So I restarted the process, this time with the InteractiveAuth switch, and to my surprise, it didn't work!
"C:\Program Files\Microsoft Azure Active Directory Connect\AzureADConnect.exe" /interactiveauth
Since I was at the same place as before, I've decided to try to make sure I use TLS 1.2 on the server. It seems all the new services require TLS 1.2, and if you've been using your server for a while, that's not a default setting. I had a similar problem four years ago when PowerShellGallery was broken due to the TLS 1.2 change I blogged about. You can read about it here. Setting proper registry settings the way to go:
Set-ItemProperty `
-Path "HKLM:\SOFTWARE\Microsoft\.NetFramework\v4.0.30319" `
-Name "SchUseStrongCrypto" `
-Value "1" `
-Type DWord `
-Force
Set-ItemProperty `
-Path "HKLM:\SOFTWARE\Wow6432Node\Microsoft\.NetFramework\v4.0.30319" `
-Name "SchUseStrongCrypto" `
-Value "1" `
-Type DWord `
-Force
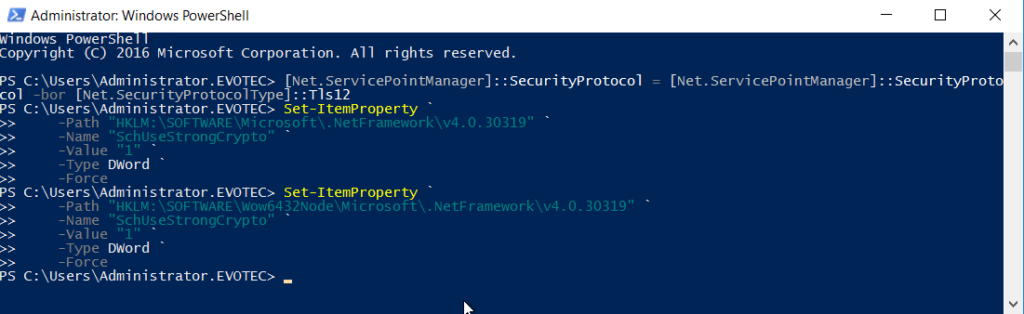
Now reboot the server, restart the upgrade process.
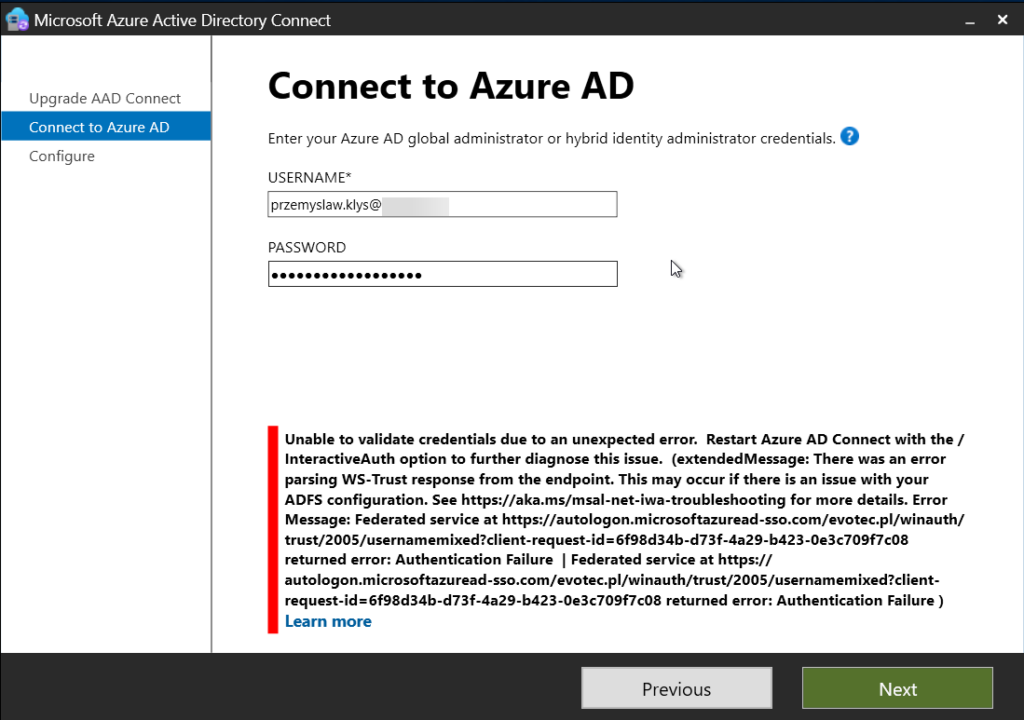
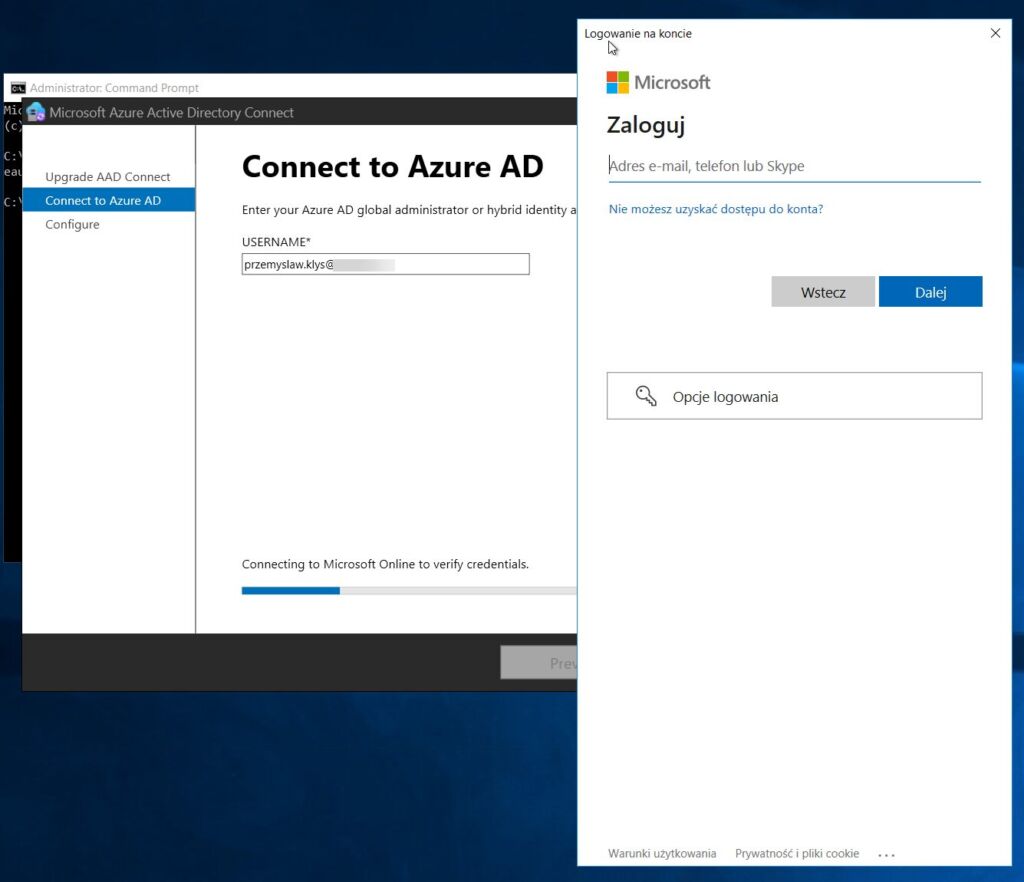
This time, the error is a bit different, so again, I suspect it's related to the MFA process on my account. Let's restart it again with InteractiveAuth.
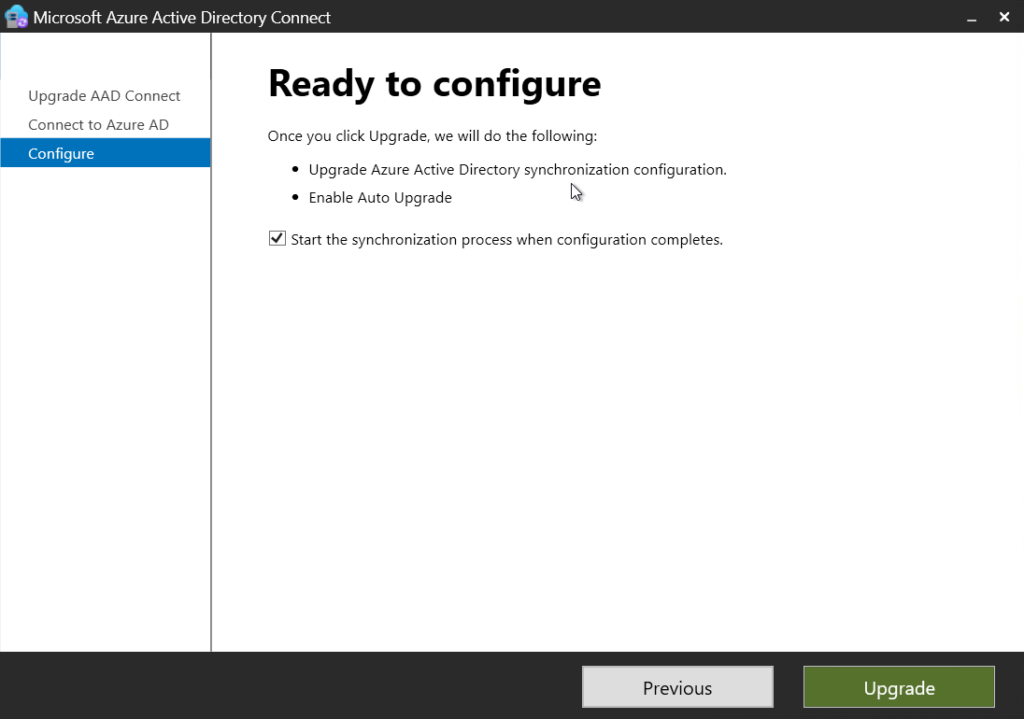
As expected, it worked much better this time, prompting me to change my password.
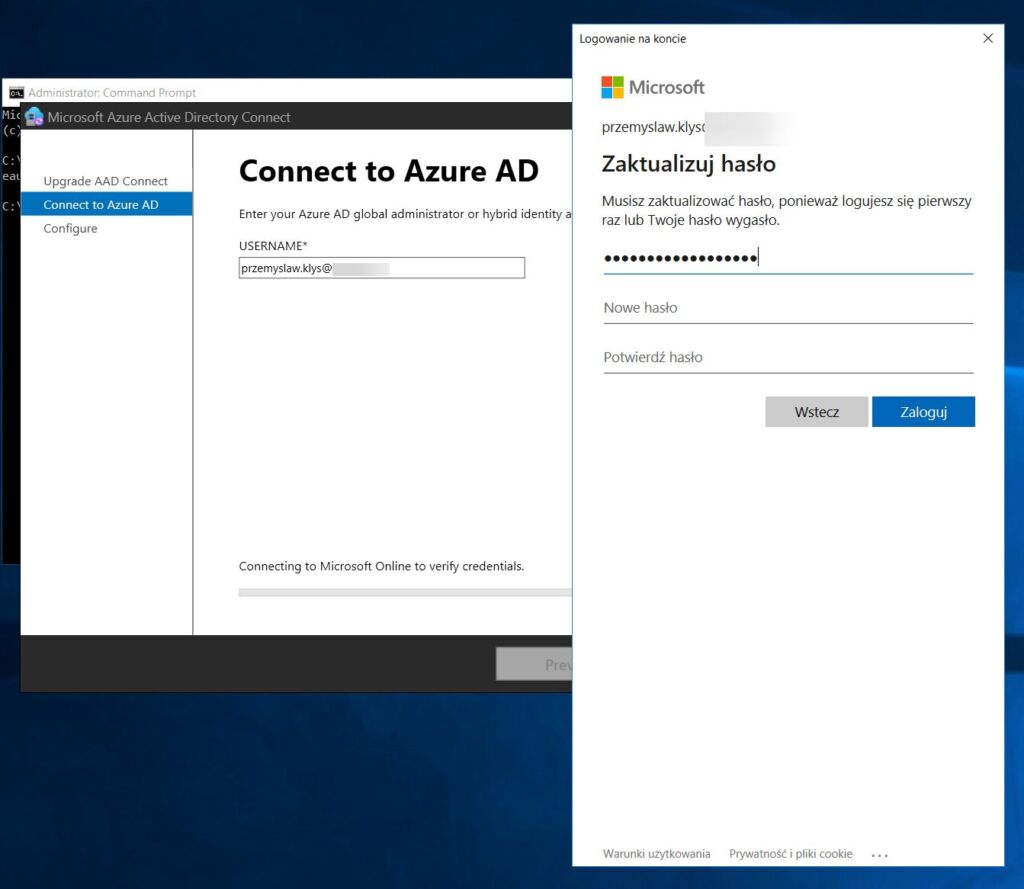
Once changed, authentication worked and I was ready for an upgrade!