blog
Testing LDAP and LDAPS connectivity with PowerShell
One of the common ways to connect to Active Directory is thru LDAP protocol. There are a lot of applications that talk to AD via LDAP. By default Active Directory has LDAP enabled but that's a bit insecure in today's world. That's where LDAPS comes in. It's not easy to set up, but when you get it done, it works. The problem I had recently is that while setting up LDAPS on DC's I only did this on some of the DC's, and not all of them as I should.
An updated version of Test-LDAP has been released along with a full-scope approach. The blog post about it can be found at Monitoring LDAPS connectivity/certificate with PowerShell. Code and blog post below is still useful tho.[/
💡 Testing LDAP and LDAPS with Powershell
Now I don't want to bore you with details why I failed to deploy LDAPS to only some of **Domain Controllers **and not all of them, but I wanted to give you an easy way to test whether LDAP, LDAPS are available and working. Why would you need it? To quickly check if your DC's work properly after setting it up. And if someone asks you about it two weeks later, you can verify it again without much effort. That way, you can learn from my mistakes and test your LDAPS functionality after you're done implementing.
function Test-LDAPPorts {
[CmdletBinding()]
param(
[string] $ServerName,
[int] $Port
)
if ($ServerName -and $Port -ne 0) {
try {
$LDAP = "LDAP://" + $ServerName + ':' + $Port
$Connection = [ADSI]($LDAP)
$Connection.Close()
return $true
} catch {
if ($_.Exception.ToString() -match "The server is not operational") {
Write-Warning "Can't open $ServerName`:$Port."
} elseif ($_.Exception.ToString() -match "The user name or password is incorrect") {
Write-Warning "Current user ($Env:USERNAME) doesn't seem to have access to to LDAP on port $Server`:$Port"
} else {
Write-Warning -Message $_
}
}
return $False
}
}
Function Test-LDAP {
[CmdletBinding()]
param (
[alias('Server', 'IpAddress')][Parameter(Mandatory = $True)][string[]]$ComputerName,
[int] $GCPortLDAP = 3268,
[int] $GCPortLDAPSSL = 3269,
[int] $PortLDAP = 389,
[int] $PortLDAPS = 636
)
# Checks for ServerName - Makes sure to convert IPAddress to DNS
foreach ($Computer in $ComputerName) {
[Array] $ADServerFQDN = (Resolve-DnsName -Name $Computer -ErrorAction SilentlyContinue)
if ($ADServerFQDN) {
if ($ADServerFQDN.NameHost) {
$ServerName = $ADServerFQDN[0].NameHost
} else {
[Array] $ADServerFQDN = (Resolve-DnsName -Name $Computer -ErrorAction SilentlyContinue)
$FilterName = $ADServerFQDN | Where-Object { $_.QueryType -eq 'A' }
$ServerName = $FilterName[0].Name
}
} else {
$ServerName = ''
}
$GlobalCatalogSSL = Test-LDAPPorts -ServerName $ServerName -Port $GCPortLDAPSSL
$GlobalCatalogNonSSL = Test-LDAPPorts -ServerName $ServerName -Port $GCPortLDAP
$ConnectionLDAPS = Test-LDAPPorts -ServerName $ServerName -Port $PortLDAPS
$ConnectionLDAP = Test-LDAPPorts -ServerName $ServerName -Port $PortLDAP
$PortsThatWork = @(
if ($GlobalCatalogNonSSL) { $GCPortLDAP }
if ($GlobalCatalogSSL) { $GCPortLDAPSSL }
if ($ConnectionLDAP) { $PortLDAP }
if ($ConnectionLDAPS) { $PortLDAPS }
) | Sort-Object
[pscustomobject]@{
Computer = $Computer
ComputerFQDN = $ServerName
GlobalCatalogLDAP = $GlobalCatalogNonSSL
GlobalCatalogLDAPS = $GlobalCatalogSSL
LDAP = $ConnectionLDAP
LDAPS = $ConnectionLDAPS
AvailablePorts = $PortsThatWork -join ','
}
}
}
While there are two functions, the first one is just a helper function. You can use Test-LDAP to verify whether LDAP and LDAPS are available on one or more Domain Controllers.
Test-LDAP -ComputerName 'AD1','AD2' | Format-Table
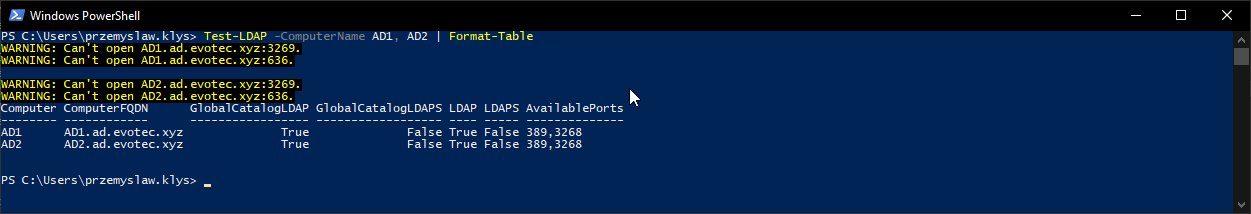
While the test is pretty “dumb” it provides an easy way to confirm whether LDAP or LDAPS are available.
💡 Using ADEssentials as PowerShell Module
For easy use and installation, I've added it to a small PowerShell Module called ADEssentials. Installing it is as easy as it gets.
Install-Module ADEssentials -AllowClobber -Force
Code as always is stored on GitHub and is free to use and take. After you install it, all commands become available without you having to do put them in a script. Bonus point is you'll get a few other functions that are useful for Active Directory management.