ImagePlayground is a PowerShell module that works in PowerShell 5.1 and PowerShell 7+. It works partially on Linux and should work on macOS, except for charts. That means it’s partially cross-platform, but the end goal is to make it work fully on all platforms. So what can this module do?
Search Results "pswritehtml"
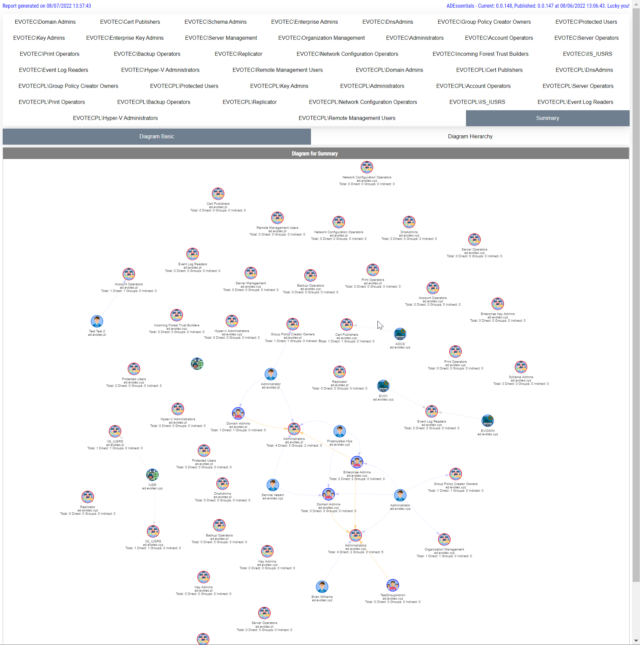
I work a lot with Active Directory-related tasks. One of the tasks is to know the group membership of critical Active Directory Groups such as Domain Admins, Enterprise Admins, Schema Admins, Event Log Readers, and a few others that are a bit less known. As I did it, I got bored of typing the group names repeatedly and decided that enough was enough and there must be an easier way for me to do that.
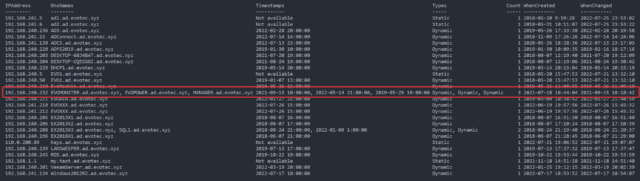
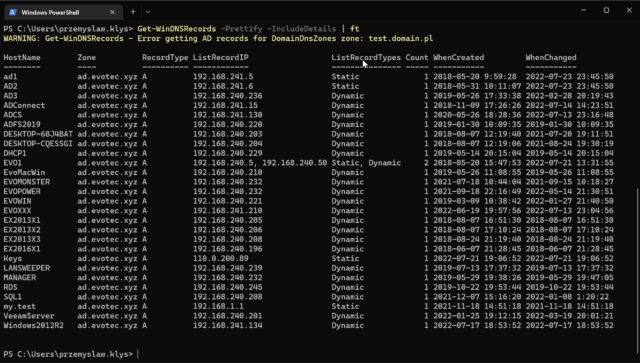
In my earlier blog post, I showed you a way to find duplicate DNS entries using PowerShell, but the focus was on finding duplicate entries based on hostname. But what if you would like to find duplicate entries based on IP Addresses? This was the question I was asked on Reddit, and I thought it was a legitimate request, so today’s focus will be on transposing table output from earlier functions to present data differently.
Today’s blog post is about Active Directory-integrated DNS and how to find duplicate entries. By duplicate, I mean those where one DNS name matches multiple IP addresses. While some duplicate DNS entries are expected, in other cases, it may lead to problems. For example, having a static IP assigned to a hostname that later on is also updated with dynamic entries.
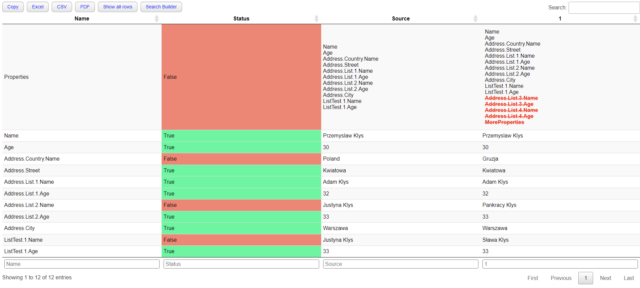
Two years ago, I wrote a blog post on how you can compare two or more objects visually in PowerShell that works on Windows, Linux, or macOS. I’ve been using that for a while, but it had a specific flaw. Comparing more advanced objects that you often see (for example, returned by Graph API, two config files) wasn’t working correctly, often throwing errors. The reason for this was that having nested hashtables arrays require more advanced logic. Today I’ve updated my module to use the ConvertTo-FlatObject function, which allows the Compare-MultipleObjects function to compare suitably more advanced objects hopefully. Of course, it should not throw errors anymore.
PowerShell language allows you to work and build complicated objects. There are multiple ways to save them, such as XML or JSON, but sometimes using them is impossible or inadequate. Sometimes you want to use HTML or CSV or any other single dimension output.
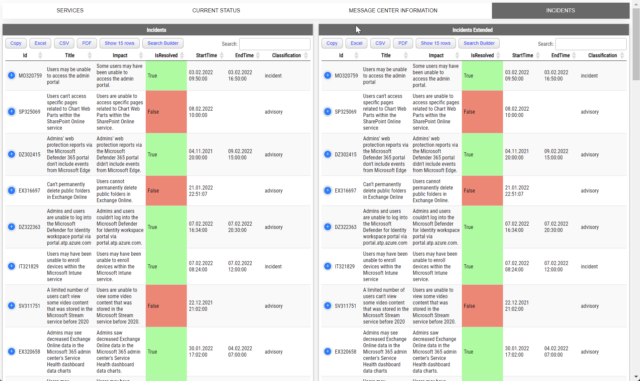
Two years ago, I wrote a PowerShell module called PSWinDocumentation.O365HealthService. The idea was simple – replicate Health Service data Microsoft offers in Office Portal so you can do with data whatever you want and display it however you like. I’ve written about it in this blog post. A few weeks back, someone reported that the module stopped working, and I’ve confirmed it indeed no longer works! Initially, I thought that maybe some data format changed, as it changed multiple times, or perhaps the date format was wrong again, but no. Microsoft has deprecated Office 365 Service Communications API reference and instead tells us that Service Health is now only available via Microsoft Graph API. Is it only me who didn’t get the memo about this?
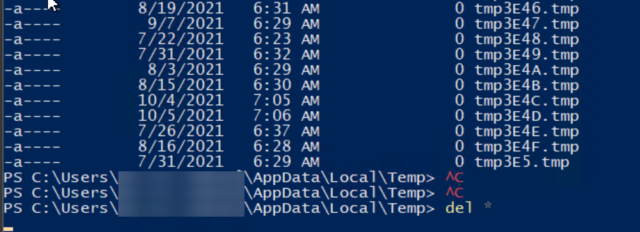
Today’s story is about me making assumptions on how things work based on the method’s name. As the blog post says, I want to focus on two similar methods – GetTempFileName() and GetRandomFileName(), when using PowerShell. Still, since those methods are .NET based, it applies to a whole range of other languages – C#, F#, VisualBasic, and all others that I’ve never used.
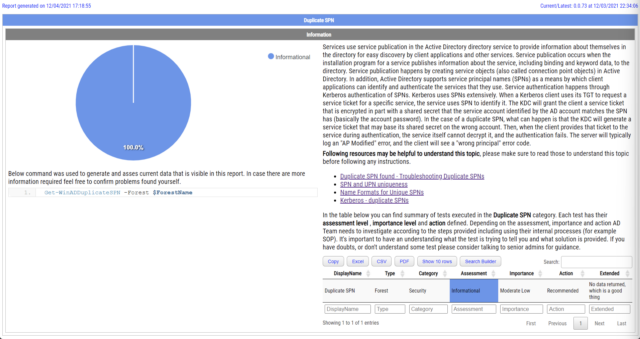
Duplicate SPNs aren’t very common but can happen in any Active Directory as there’s no built-in way that tracks and prevent duplicate SPN’s. One has to either know all SPN’s in the environment, track them or check each time whether it already exists or not. Things get more complicated with larger Active Directory environments as people change, new apps are added, old apps are forgotten, but SPNs prevail.