blog
Windows Server – How to change SHA1 to SHA256, SHA384 or SHA512 options in Certification Authority
Since SHA1 became insecure and everyone around the web is forcing the change to higher security standards such as SHA256, SHA384 or SHA512 Windows Administrators should also update their internal **Microsoft Active Directory Certificate Services **to force higher cryptographic provider.
🔒 Solution
There are 2 things that needs to be done to secure your CA servers.
First one is to change internal CSP for the servers by using following commands:
Microsoft Windows [Version 6.3.9600]
(c) 2013 Microsoft Corporation. All rights reserved.
C:\Windows\system32>certutil -setreg ca\csp\CNGHashAlgorithm SHA256
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\CertSvc\Configuration\\csp:
Old Value:
CNGHashAlgorithm REG_SZ = SHA1
New Value:
CNGHashAlgorithm REG_SZ = SHA256
CertUtil: -setreg command completed successfully.
The CertSvc service may need to be restarted for changes to take effect.
C:\Windows\system32>net stop certsvc
The Active Directory Certificate Services service is stopping.
The Active Directory Certificate Services service was stopped successfully.
C:\Windows\system32>net start certsvc
The Active Directory Certificate Services service is starting.
The Active Directory Certificate Services service was started successfully.
C:\Windows\system32>certutil -getreg CA\CSP\CNGHashAlgorithm
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\CertSvc\Configuration\\CSP:
CNGHashAlgorithm REG_SZ = SHA256
CertUtil: -getreg command completed successfully.
Those commands should be executed on all your CA servers (CA Root and CA Issue)Second place to change settings is to modify templates that are used by users / administrators to generate new certificates.
Open up Certificate Templates
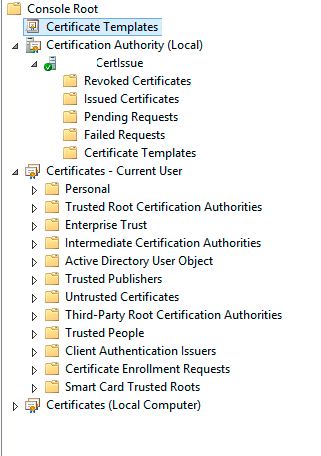
Find certificate you want to update
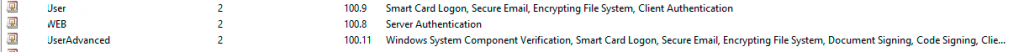
Open up certificate template you need to change
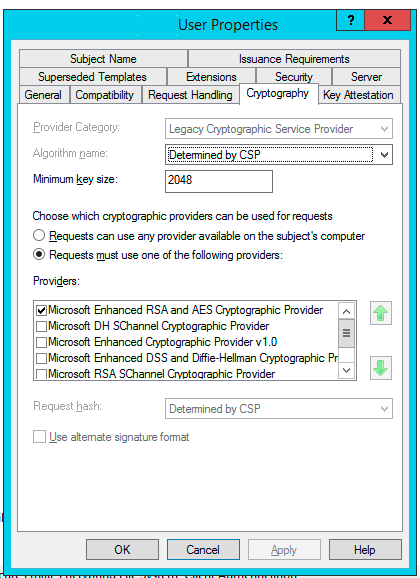
Make sure that Microsoft Enhanced RSA and AES Cryptographic Provider is selected.
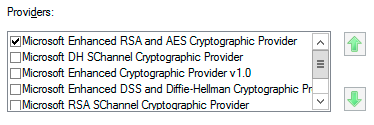
You can of course have multiple providers selected but if you want to limit user choice select only one. Save settings and you're good to go!Now when you go to website to generate new certificate https://<YourCertServer.corp/certsrv/ simply choose Request a certificate
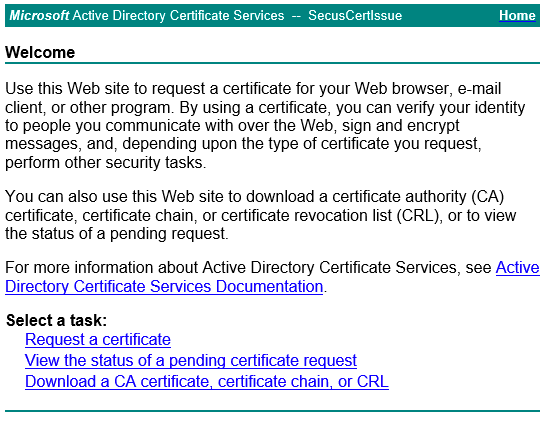
After choosing new certificate, we have to pick the modified Certificate Template
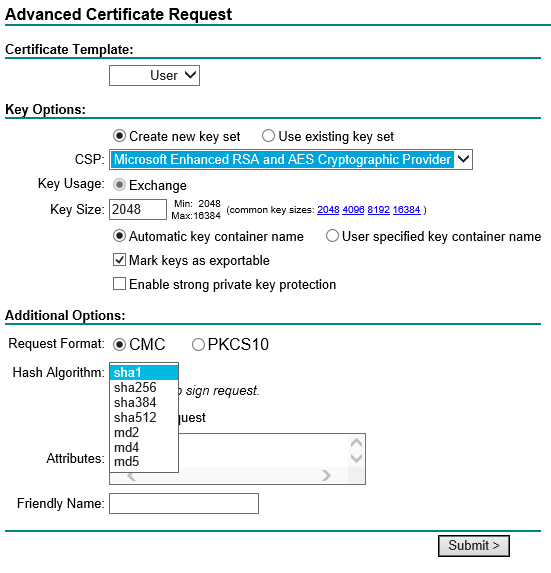
And under Hash Algorithm new options from SHA1, thru SHA256, SHA384, SHA512 to finish up on MD5. If you don't see those options make sure under CSP provider** ****Microsoft Enhanced RSA and AES Cryptographic Provider **is chosen. And you're good to go!