blog
Delegating Active Directory attribute physicalDeliveryOfficeName
Being responsible for Active Directory you're often tasked with fairly simple task of delegating permissions for user and groups. After doing it multiple times you know how to do it, but then you're told to delegate only one attribute physicalDeliveryOfficeName and things get complicated.
❗ Problem Description
Normally delegating attributes in Active Directory is simple walk in a park.
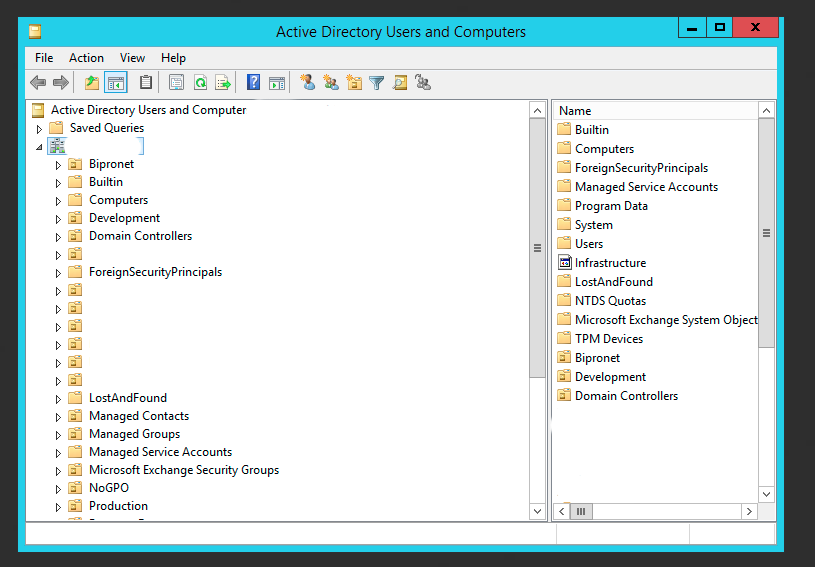
- You open up Active Directory Users and Computers
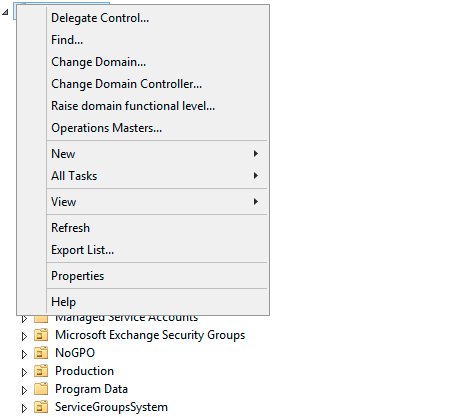
- Right click on click on root of the domain or the object you want to delegate permissions on choose Delegate Control…
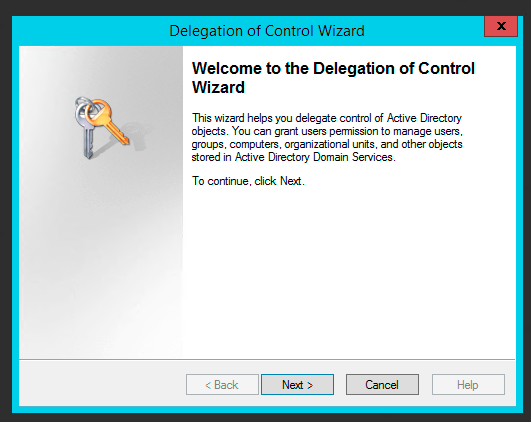
- Follow Delegation of Control Wizard
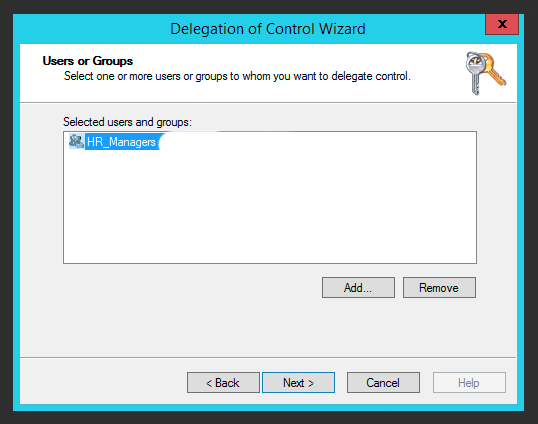
- Select User or Groups to delegate permissions to (obviously choose Groups)
- Choose Create a custom task to delegate
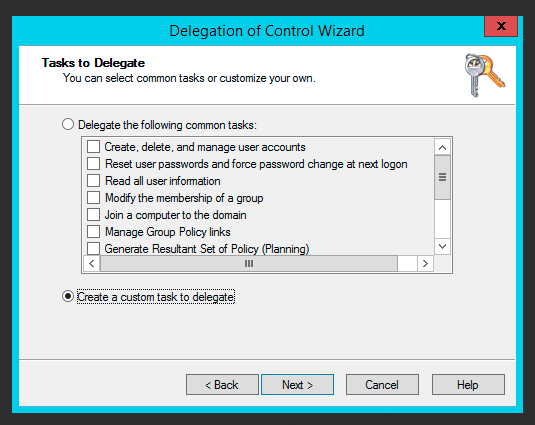
- Choose Only the following objects in the folder, and select User objects
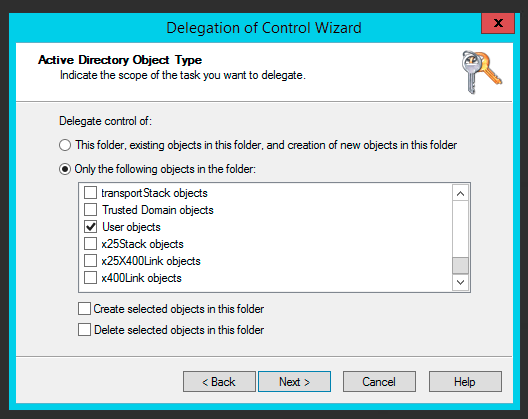
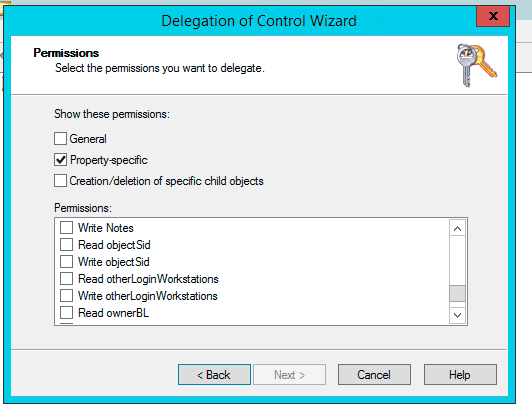
- And then, uncheck General, choose** Property-Specific** and find your precious property such as physicalDeliveryOfficeName that you were looking for on the list.
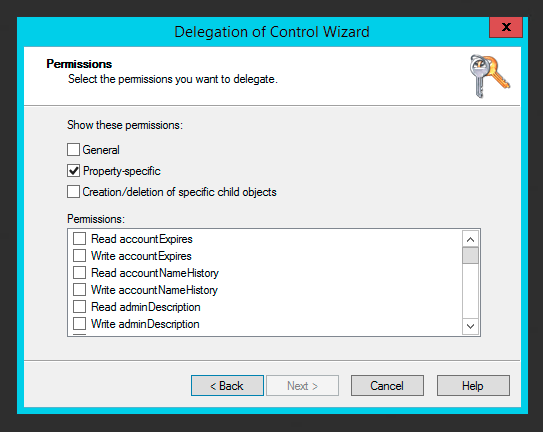
- The only problem… it's not on the list. So you cancel, and go for the more direct approach.. modifying security properties directly.
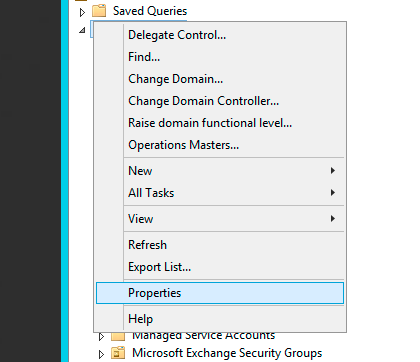
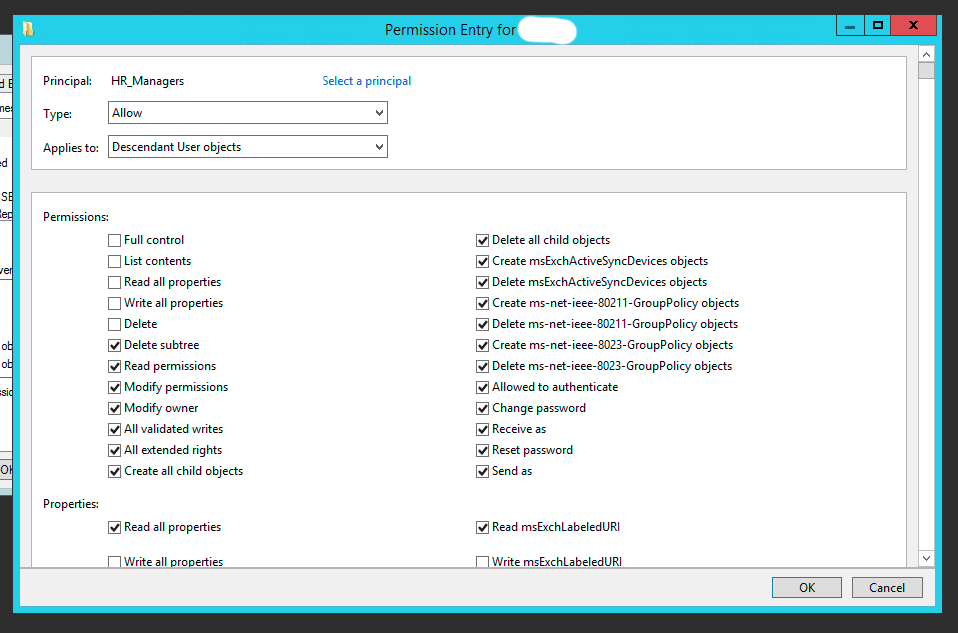
- You choose **Properties, **go to **Security **tab and press Advanced.

- Then you choose Add permission, you choose your principal group, you choose Type to Allow, Applies to: Descendant User objects… finally you uncheck not needed permissions, and then you find there's no such field as **physicalDeliveryOfficeName **on that list!
✅ Solution
As bad as it sounds I was really stomped. Either I am blind or something is seriously missing. It turns out it is missing and unless you enable it it's gonna stay invisible. The solution is quite simple:
- Close all instances of Active Directory Users and Computers
- Open Windows Explorer and go to C:\Windows\System32 and find dssec.dat file
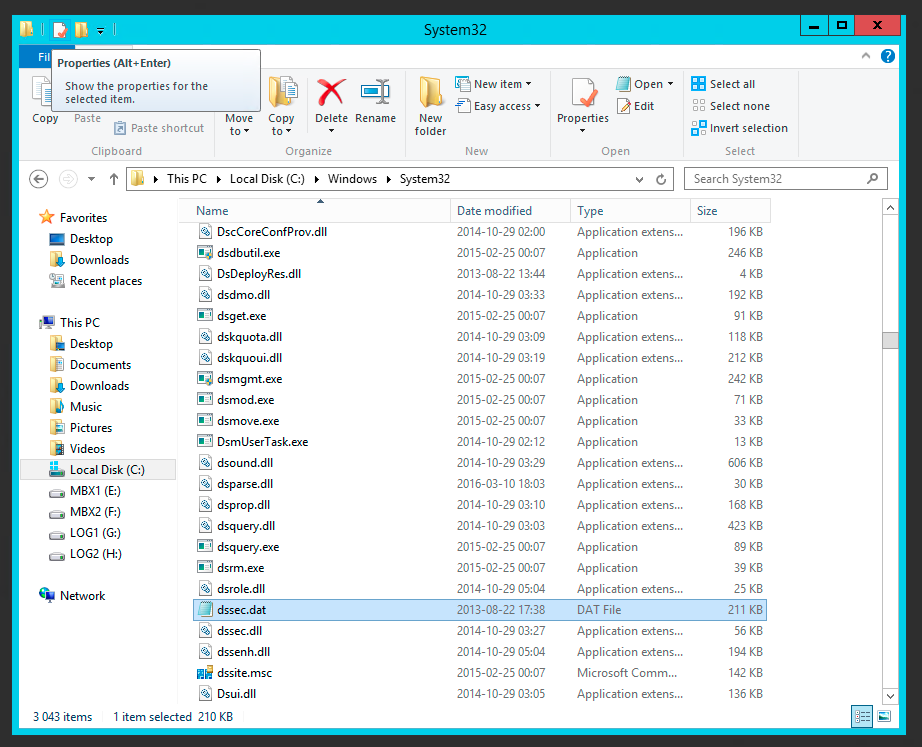
- Make yourself a copy of that file in case things get ugly. The file holds settings for each value for that is supposed to be filtered out of delegation/security tabs.
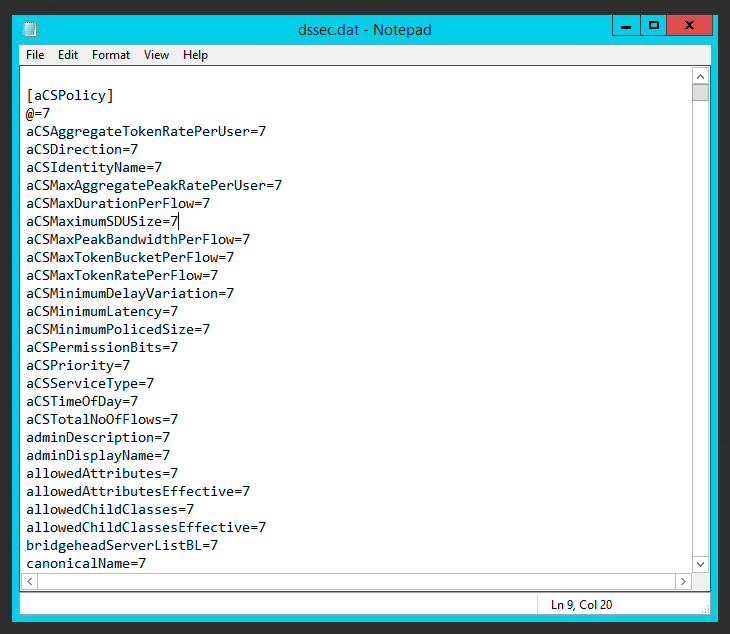
- Find** [user]** section (or any section you want that property to be visible at and change physicalDeliveryOfficeName=7 to physicalDeliveryOfficeName=0.
- Now open up Active Directory Users and Computers and it should be there… although not in the form you expected it. The property is called Office Location.
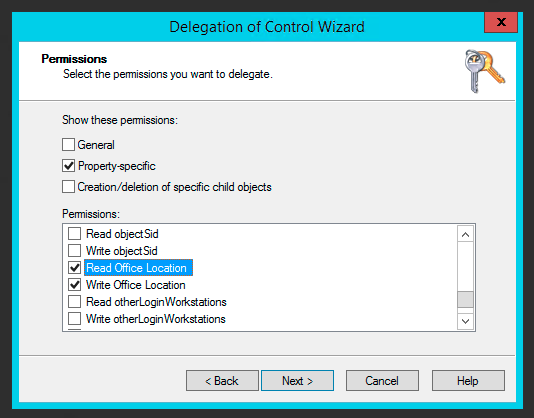
- And if you're wondering now if it was there all along.. well I did wonder myself so I've checked on different AD controller… and as you can see below it's not there.
📝 Notes
The Per-Property Permissions tab for a user object that you view through Active Directory Users and Computers may not display every property of the user object. This is because the user interface for access control filters out object and property types to make the list easier to manage. While the properties of an object are defined in the schema, the list of filtered properties that are displayed is stored in the Dssec.dat file that is located in the %systemroot%\System32 folder on all domain controllers. You can edit the entries for an object in the file to display the filtered properties through the user interface. A filtered property looks like this in the Dssec.dat file:
[User] propertyname=7
To display the read and write permissions for a property of an object, you can edit the filter value to display one or both of the permissions. To display both the read and write permissions for a property, change the value to zero (0):
[User] propertyname=0
To display only the write permission for a property, change the value to 1:
[User] propertyname=1
To display only the read permissions for a property, change the value to 2:
[User] propertyname=2
After you edit the Dssec.dat file, you must quit and restart Active Directory Users and Computers to see the properties that are no longer filtered. The file is also machine specific so changing it on one machine doesn't update all others. It's up to you whether you want it visible everywhere or not.